
Better usability and .NET Analytic features in VB Decompiler 11.7
A lot of time has passed since the release of the previous version and today I really have something to surprise you! The new version of the decompiler has embodied a lot of little things that significantly increase the convenience of code research. And this functionality has been expected and will be appreciated by absolutely everyone. But first things first.
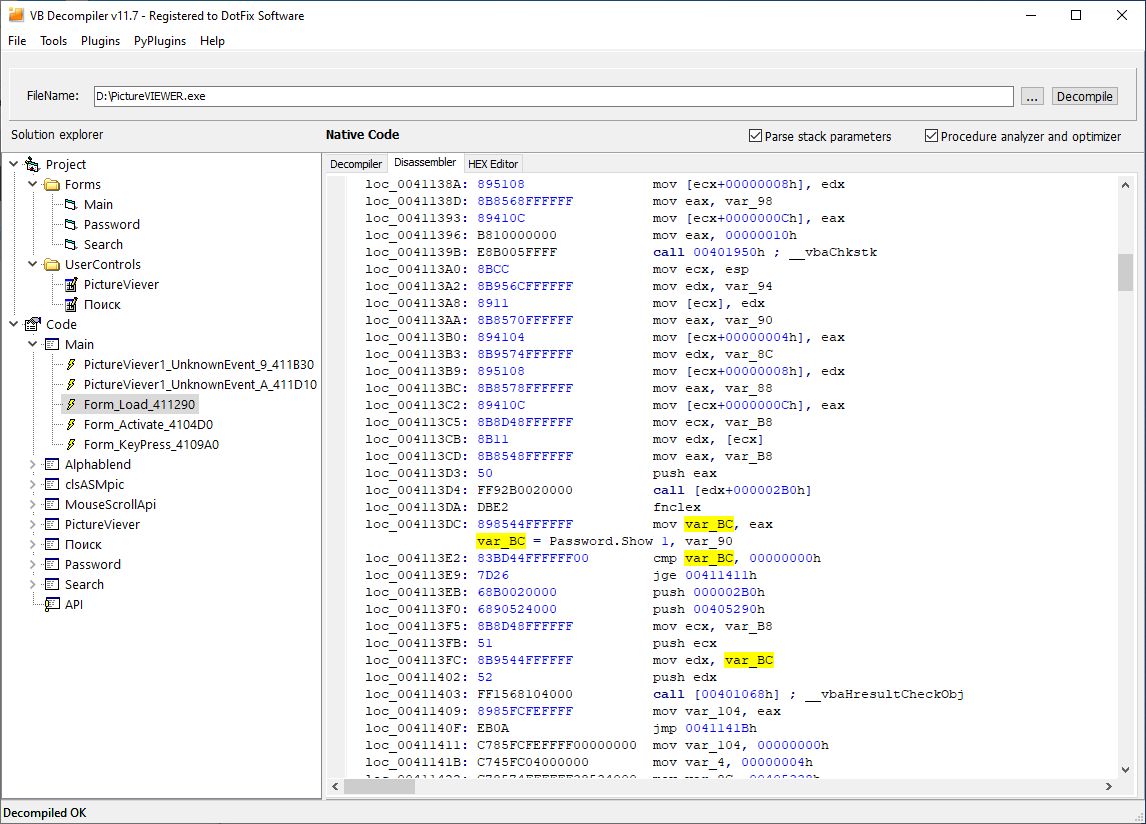
Highlighting the current command, register or variable
Yes, this functionality has been expected for a long time. But what can I say, I was waiting for this thing myself and it's incredibly comfortable. Now, by placing the cursor on one or another register, the name of a variable or function, or whatever - similar names will be highlighted throughout the code listing! And yes, when highlighting different objects, nothing slows down anywhere, nothing glitches. In general, it works exactly the way you want to see it. And it doesn't matter if you've opened the function for a couple of screens or if it's a couple of megabytes of code that can be scrolled for several minutes. Everything works fast! And I think this is the first and most important thing to be told about in the new version of VB Decompiler.
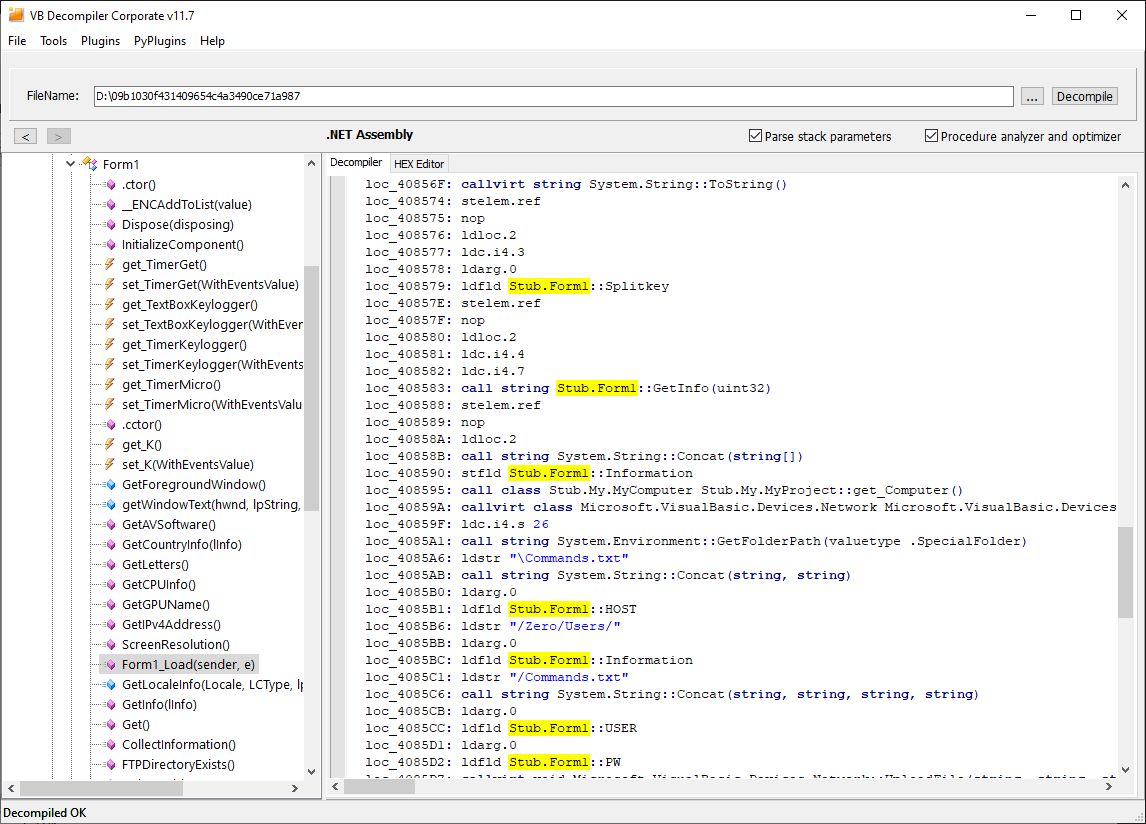
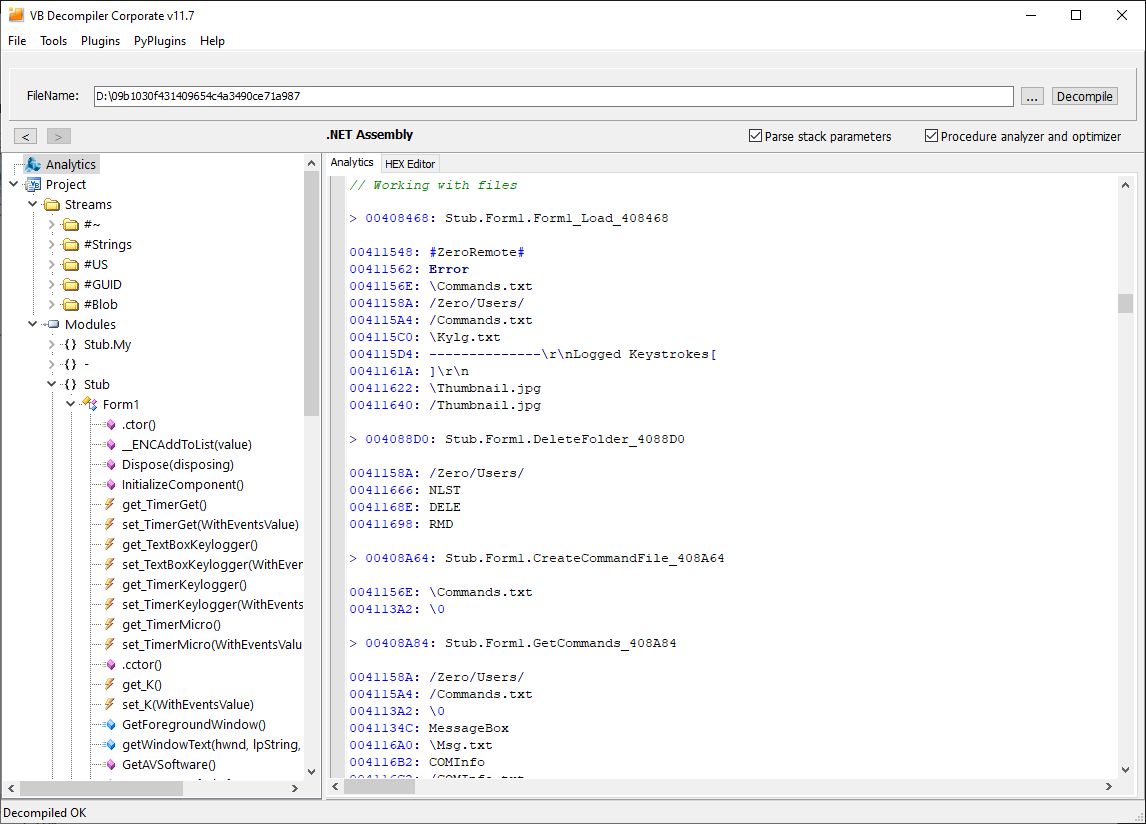
Analytic Features is now available for .NET applications
It's no secret that VB Decompiler supports disassembling .NET applications. And it doesn't matter if it is built for 32 or 64 bit Intel architecture. It doesn't matter what language is used in the program code - Visual Basic, C# or something else. Moreover, it doesn't matter if the code is Managed or Unmanaged. Both IL and x86 and x64 assemblers are supported!
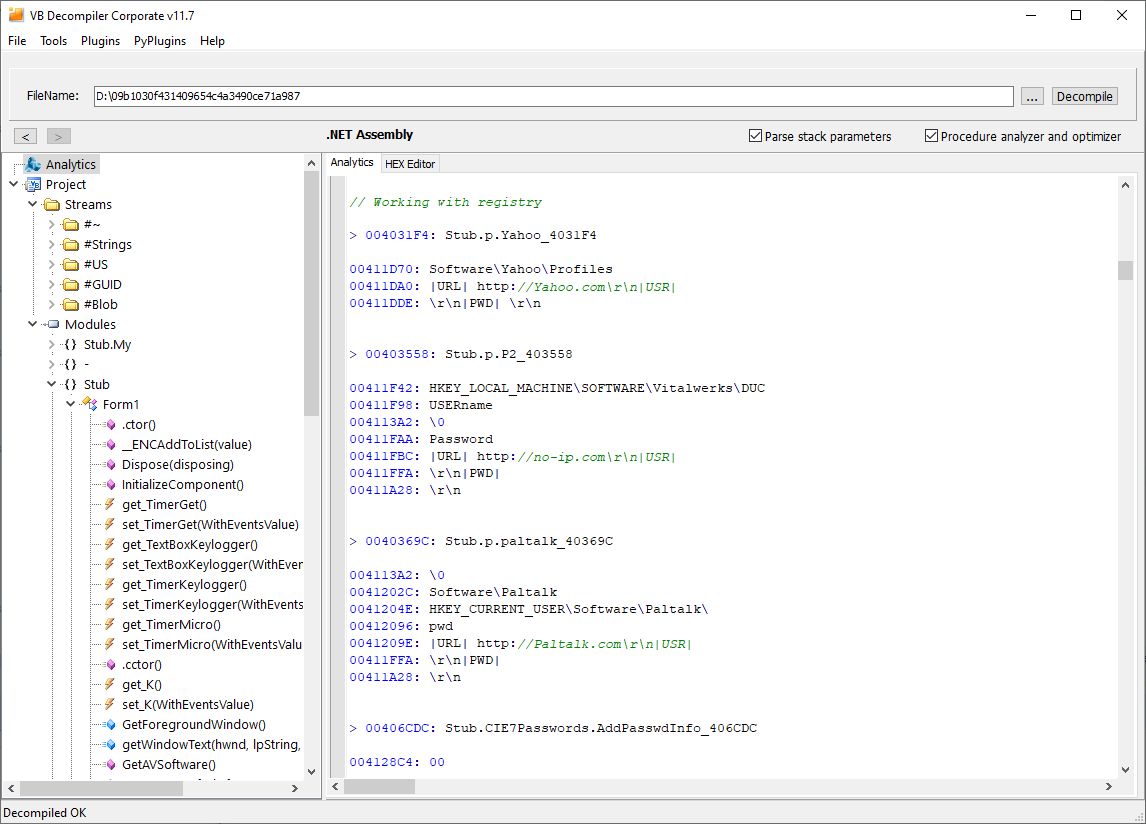
And now Analytic Features are available for .NET too! Now, like the VB5/6 application, an antivirus analyst can open any .NET malware (trojan, virus, other malicious code) in VB Decompiler and immediately get a full report on the functions that perform any critical operations: working with files, registry, internet, databases and much more.
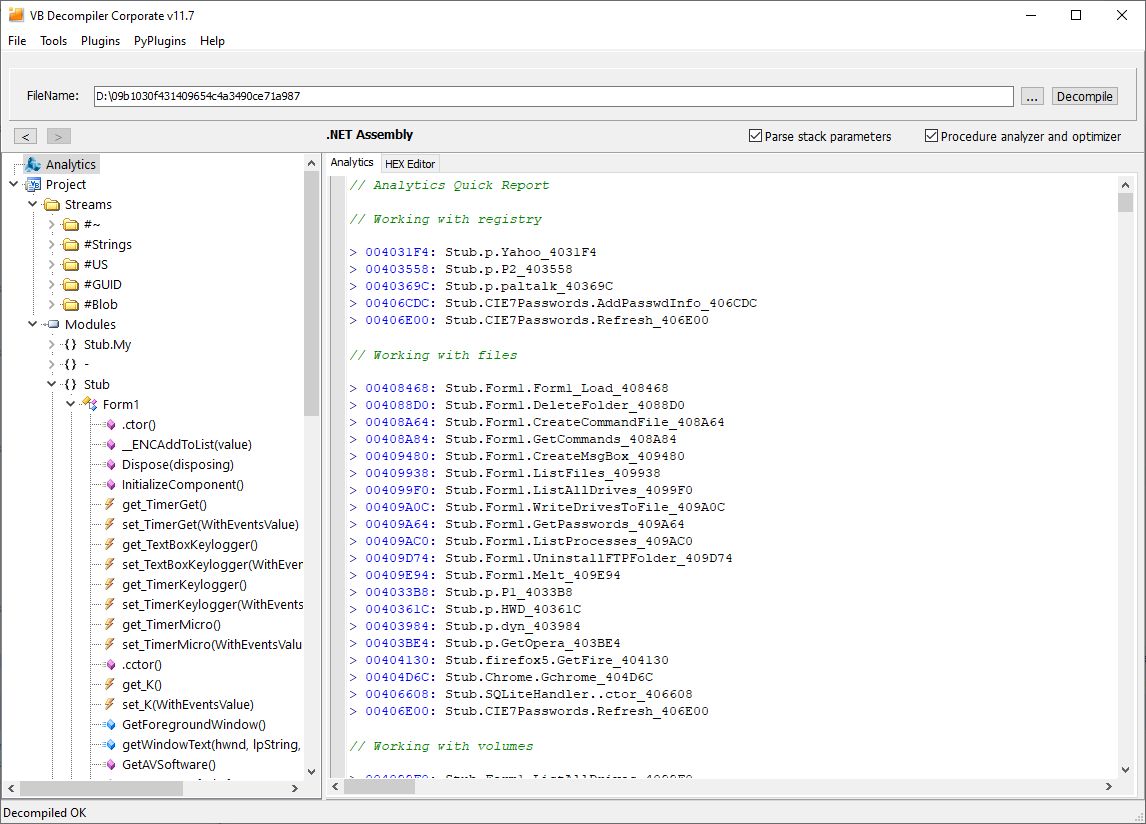
By tradition, such a report is divided into two parts: a dry list of clickable functions for a particular category and the same list, but with a list of strings used in each such function! The second list is usually more than enough to understand where and what is happening in the malware without opening the code!
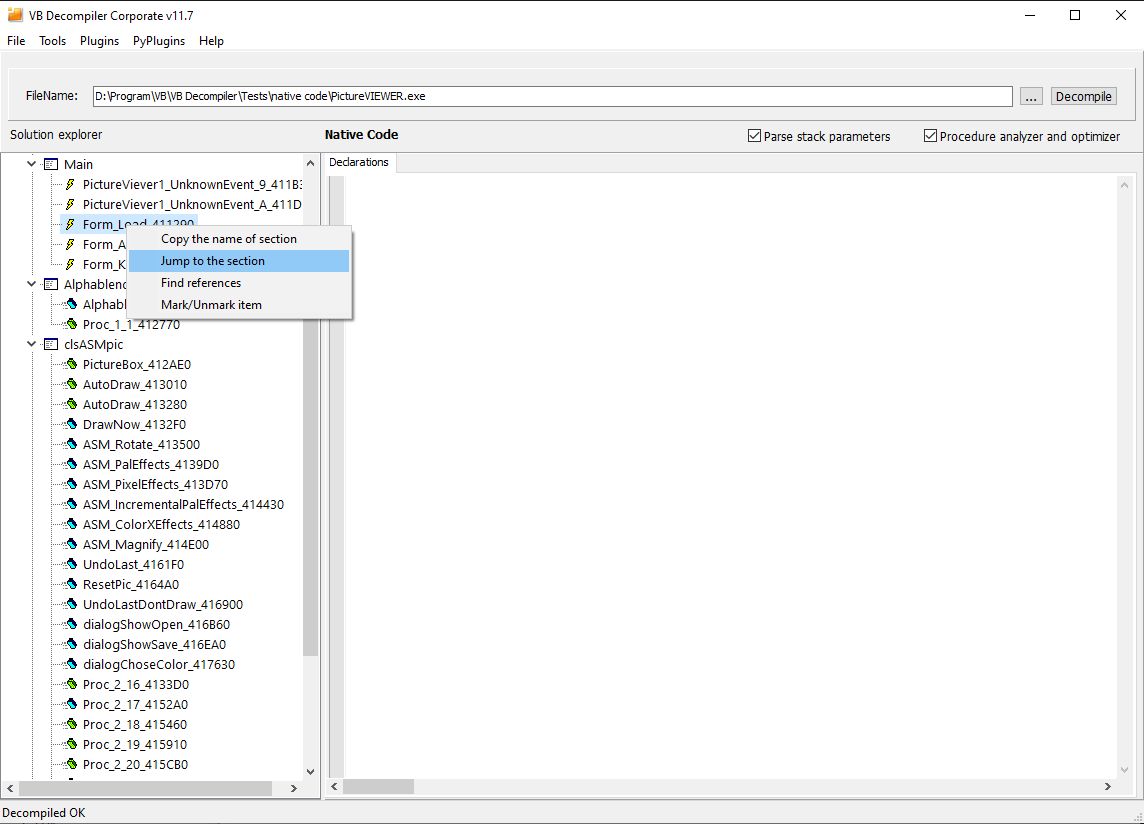
Jump to the desired function along its path
The files under study are different. Sometimes these are 3 forms and 5 classes. And here everything is quite simple. But when it is 480 forms and for a thousand modules and classes, then in this case, having finished the analysis in class 348 and 89 function, finding it the next day is oh, how difficult it is. And even knowing the name of the class and the function, just scroll the entire tree, peering at the names, the process is extremely inconvenient. I knew about the problem and now it has been solved! The object tree now has a function "Jump to the section", which works in conjunction with "Copy the name of section". Just copy the path to a particular code and go to it at the right time in two clicks!
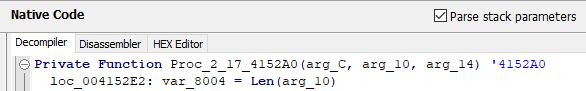
Defining the return value for private functions
The most difficult part of the work of any decompiler is the analysis of the prototype of a particular code. Is it a function or a procedure? And if a function, how many parameters does it return? Unfortunately, for Visual Basic it is possible to get this information from metadata only for Public functions of classes and forms. Private functions, as well as any in modules, are stored without any metadata. VB Decompiler has long had its own algorithms for finding such functions and analyzing their prototypes. This functionality has also been redesigned in the new version. The analyzer has been retrained with new variations; many comparisons and tests have been carried out on various optimizations. Now this functionality works much better. Moreover, already in the process of parsing public functions metadata previously unknown to the decompiler.
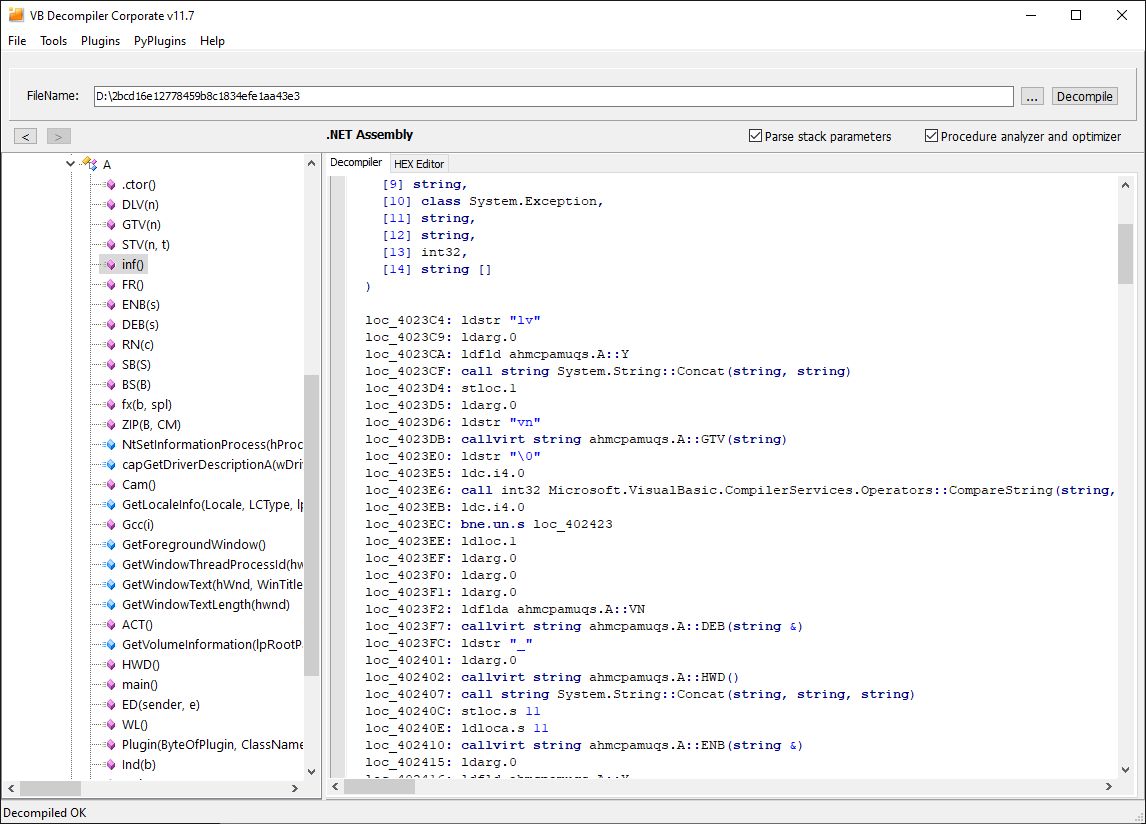
Working on .NET tables and metadata
To develop the Analytics Features for .NET code, the quality of the disassembler listings had to be significantly reworked. The decompiler now knows references to various kinds of previously unused tables. Supports parsing of the full prototype of class methods and properties. It knows about the parameters of the called functions and their types, and also supports the processing of even more severely obfuscated and crookedly dumped files! Naturally, work with crooked dumps is never guaranteed, but when you open a file in VB Decompiler that crashes in other products, you should know that this is not the "luck", but a huge amount of work that is constantly being done in this direction.
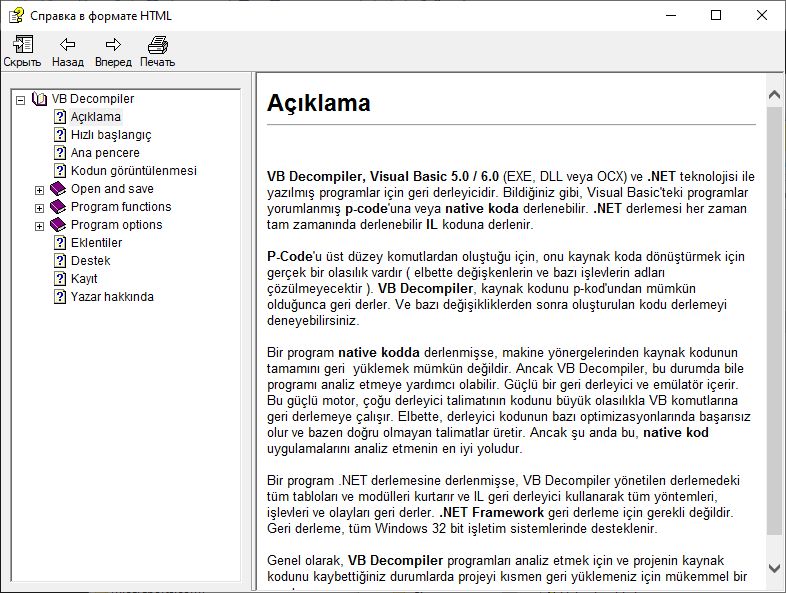
Hebrew and Turkish localizations
In this version of the decompiler, there are two new localizations from our beloved users. And according to tradition, this is not just a translation of menus and buttons. As always, it is also a translation of documentation! All available localizations, as always, are available for selection at the stage of product installation, as well as in the Options of the decompiler itself. If desired, the documentation files can always be viewed manually - chm files are available directly in the directory where the product is installed.
Improvements and fixes
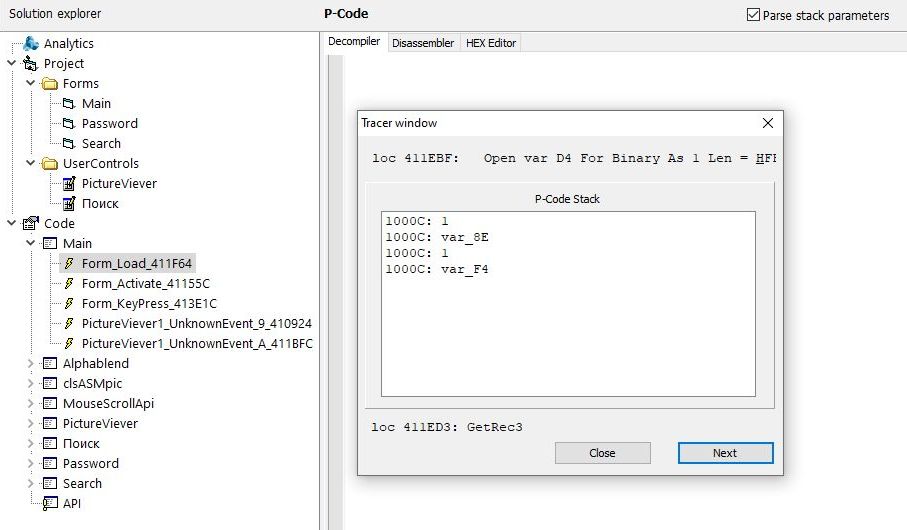
And by tradition, a lot of things has been improved and fixed. Additional syntax highlighting handlers have been made for different types of strings (for VB5/6 and for .NET) to support different types of insertion of service characters into strings. Improved P-Code Tracing Features. Double and triple passes are now taken into account during processing. A more accurate analysis of the number of arguments of public functions has been done. Due to the peculiarities of GoSub, the addresses in the Return links shifted by one byte - fixed. The FPU emulator has been improved. And also a very serious amount of fixes was made to the Procedure analyzer and optimizer, which is responsible for simplifying and folding blocks of decompiled code, making it more readable.
I sincerely hope that you enjoy the new version as much as I do. Thank you for staying with us!
November 18, 2021
(C) Sergey Chubchenko, VB Decompiler's main developer